SPONSORED POST
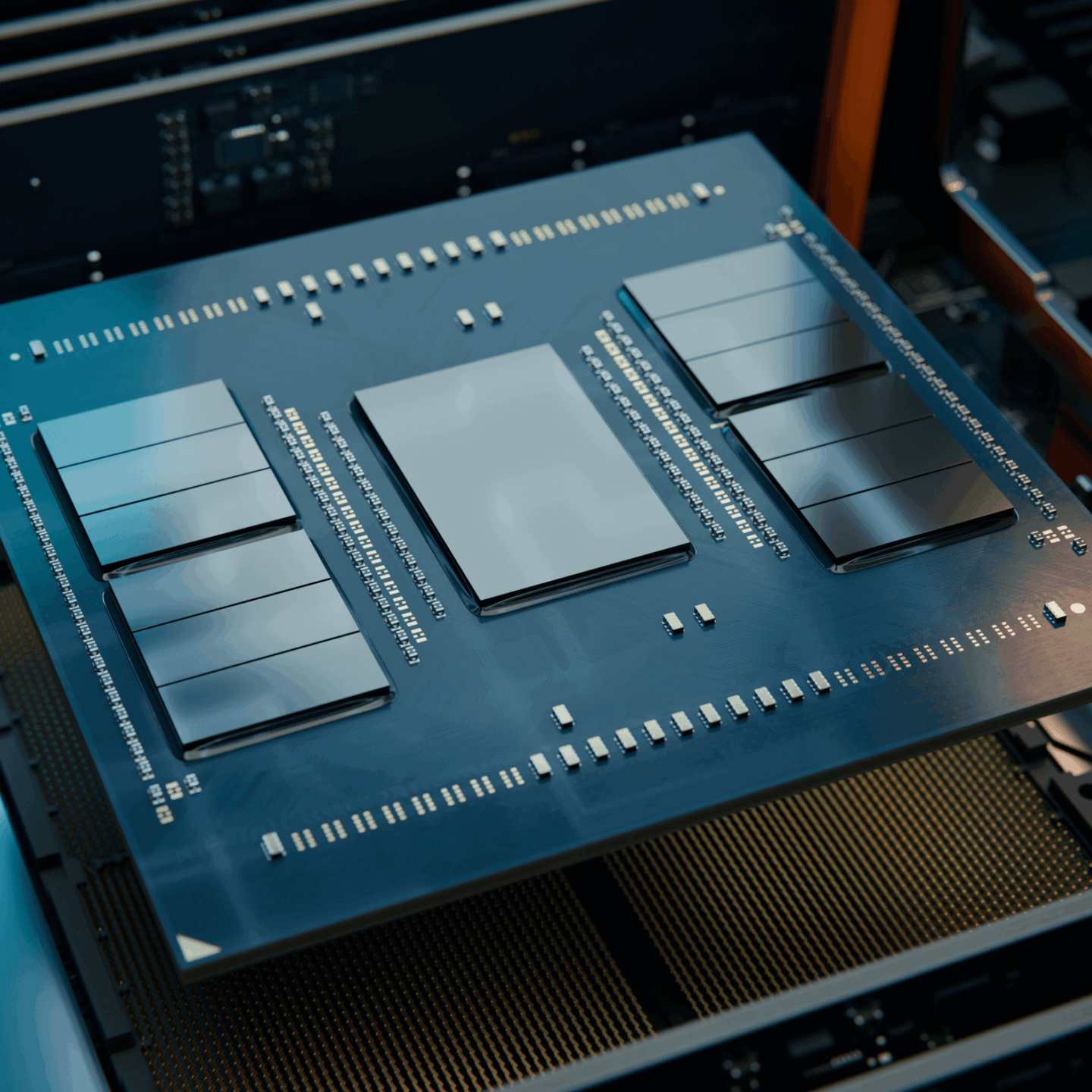
AMD Infinity Guard is a sophisticated suite of system-level security features designed for a data-driven world. Built into AMD EPYC™ processors, its state-of-the-art capabilities are designed to secure data-in-use, an increasingly popular target for bad actors.
The opportunity: Data generation is skyrocking
Data drives revenue growth for many companies and its value has never been higher. It is also fueling the social media, AI, and collaborative applications that make our data-driven world go round.
The risk: Threats to data security are growing – and evolving
Next-generation high speed networks, AI, and cloud computing all introduce new risks and vulnerabilities to data. Bad actors have also recently focused their attacks on data-inuse, while being processed by the CPU, which has historically been an overlooked concern.
The answer: AMD Infinity Guard – protect, detect, comply
Built-in at the silicon level, AMD Infinity Guard transforms server systems into a foundation of enterprise and cloud security features in a data-driven world. Its state-ofthe-art capabilities help provide protective layers around data to help mitigate internal and external threats and track it for compliance purposes.
3 ways AMD INFINITY GUARD helps protect your data
- Confidential Computing
Secure Encrypted Virtualization (SEV) technologies help keep data protected while it is being processed—not even cloud service providers have access. This is the basis of confidential computing—only the person or service that “owns” the data can decrypt it. - Shields system memory from snooping, even in the cloud
Security threats from inside an organization’s walls are a major risk. Secure Memory Encryption (SME) helps protect against attacks on the integrity of main memory from bare metal to the cloud, such as certain cold-boot attacks. - Boots only what you want to boot
AMD Secure Boot is designed to allow only authorized firmware to be booted. This defense-in-depth feature aims to provide a strong defense in response to growing firmware-level attacks.

Marco Matthias Marcone
Head of Marketing, RNT Rausch GmbH
Know-how about digitalisation, servers and storage

NIS2 made easy: Immutable storage contributes to compliance
The new NIS2 Directive presents companies with the challenge of enhancing their cybersecurity measures and ensuring data integrity. With immutable storage, businesses can ensure that critical data is permanently protected and cannot be altered. This technology not only provides increased security but also meets the stringent requirements of NIS2.
Discover how immutable storage can help your company comply with the directive while safeguarding your sensitive information.
Server clusters – the future of IT?
Who would disagree: Full power and a reliable IT infrastructure are essential…
How modern hardware is
revolutionising AI infrastructures
Modern AI infrastructures benefit immensely from the finely tuned combination…
Modern Work 2: No signal, now what?
What does a film crew do if they have no or only a poor network signal at the…
CloudFest 2026
23rd–26th March 2026 RNT Rausch and Pyramid Computer showcase innovative…
Hello Europe
At RNT we design hardware which enables software to unleash its full potential.…
SSD, HDD, NVMe and MACH.2: the truth about modern storage technologies
SSD, HDD, NVMe or MACH.2? Discover the differences, benefits and use cases of…